- Network-level — the Secure Model Protocol encrypts all communication and authenticates both parties via mTLS and on-chain identity
- Execution-level — models run in isolated containers with no direct code access; only API-based inference is exposed
- Hardware-level — Trusted Execution Environments (TEE) and Multi-Party Computation (MPC) provide additional guarantees for the most sensitive use cases
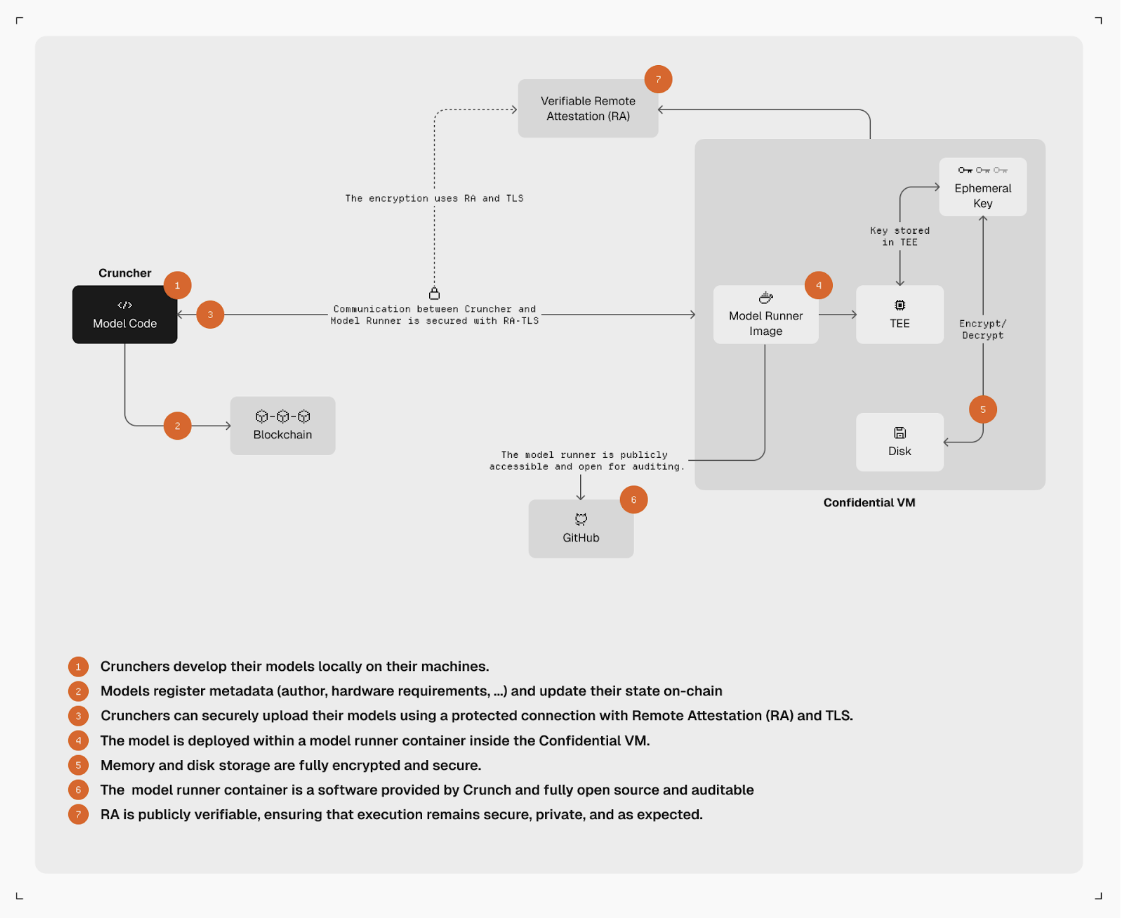
Trusted Execution Environments (TEE)
In cooperation with Phala Network, Model Runners can run inside Trusted Execution Environments. TEEs provide hardware-enforced isolation — even the infrastructure operator cannot inspect the model code or data inside the enclave. This ensures:- Model code is encrypted at rest and in transit
- Inference happens inside a tamper-proof enclave
- The Coordinator can verify the enclave’s integrity via remote attestation
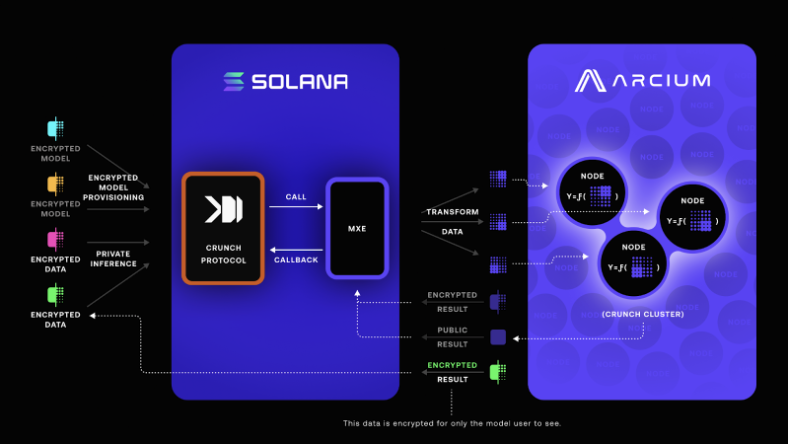
Multi-Party Computation (MPC)
In cooperation with Arcium, the protocol is exploring Multi-Party Computation for scenarios where even the model runner should not see the full input data. MPC splits computation across multiple parties so that no single party has access to both the model and the data in cleartext. This is particularly relevant for:- Competitions using proprietary enterprise data
- Healthcare and financial use cases with regulatory requirements
- Scenarios where Coordinators want to protect raw data from model authors
Next: Tournament Hub
Where participants discover and join your competition.